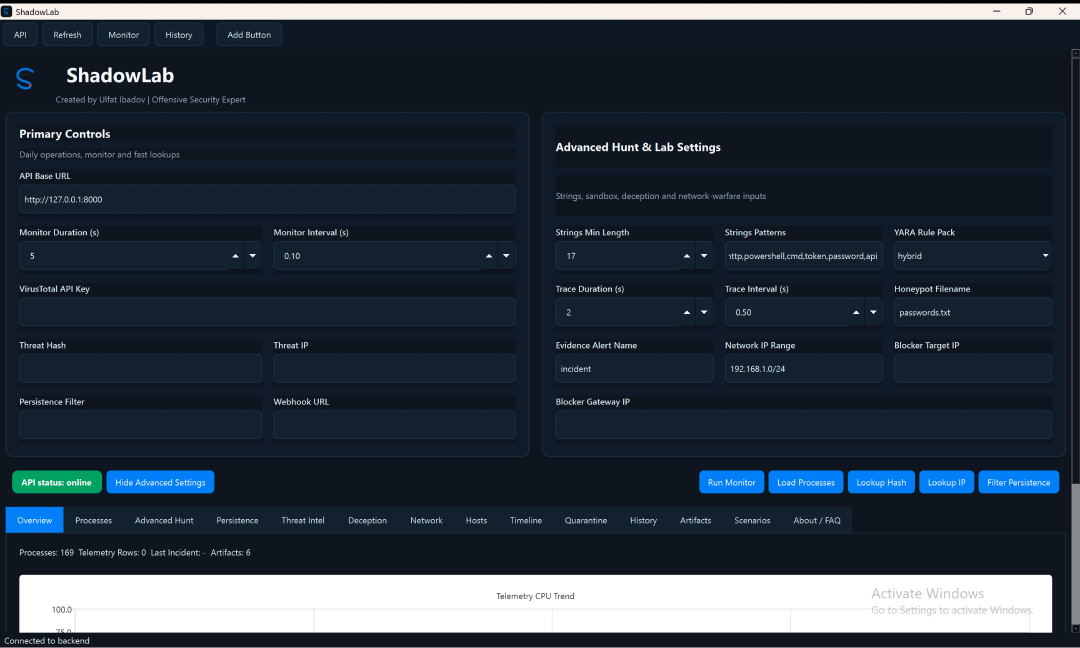
Live operator surface
Windows Defensive Research Platform
Investigate behavior,
trace signals,
drive response.
ShadowLab is an API-first cybersecurity platform for threat hunting, process intelligence, YARA inspection, persistence analysis, timeline review, quarantine control, and operator-driven response.
- FastAPI API-first backend
- PySide6 Native desktop shell
- Threat Intel VT, MalwareBazaar, AbuseIPDB
Threat intel
Hash reputation
- MalwareBazaar lookup
- Process hash auto-fill
- Verdict history
Response layer
Quarantine & timeline
- Incident updates
- Artifact tracking
- Kill-tree and remediation
A product surface built around the analyst workflow, not just a dashboard.
01
Process Intelligence
Inspect process metadata, command-line behavior, SHA-256, signature state, internals, strings, YARA hits, and sandbox traces from one operator surface.
02
Threat Intel Enrichment
Run hash and IP lookups with external intelligence sources and keep verdict history inside the workflow rather than jumping across tools.
03
Persistence & Deception
Review persistence points, trigger remediation, deploy honeypots, manage canaries, and capture evidence artifacts during high-signal events.
04
Timeline, Incidents, Quarantine
Move from a raw detection to response with timeline context, incident status, ownership, quarantine actions, and exportable artifacts.
From detection signal to response action.
Detect
Telemetry, process scans, YARA, strings, and hunt modules surface suspicious activity.
Investigate
Threat intel, process internals, network context, and memory workflow deepen the signal.
Triage
Incidents, severity, ownership, and timeline context support fast analyst decision-making.
Respond
Quarantine, kill-tree, persistence remediation, and evidence collection close the loop.
Each view maps to a concrete part of the defensive workflow.
Overview
High-signal operational entry point
Hero controls, telemetry trend, API state, and operator tabs are presented as one tactical surface instead of a fragmented utility interface.
Processes
Deep process analysis without leaving the workspace
Auto triage, memory analysis, internals, strings, YARA, sandbox trace, AI analyst summaries, and response controls stay close to the selected process.
Intel / Response / Hunt
Cross-functional panels for real workflows
Threat intel, network capture, deception, hosts, timeline, history, artifacts, quarantine, and persistence are exposed as first-class operator tools.
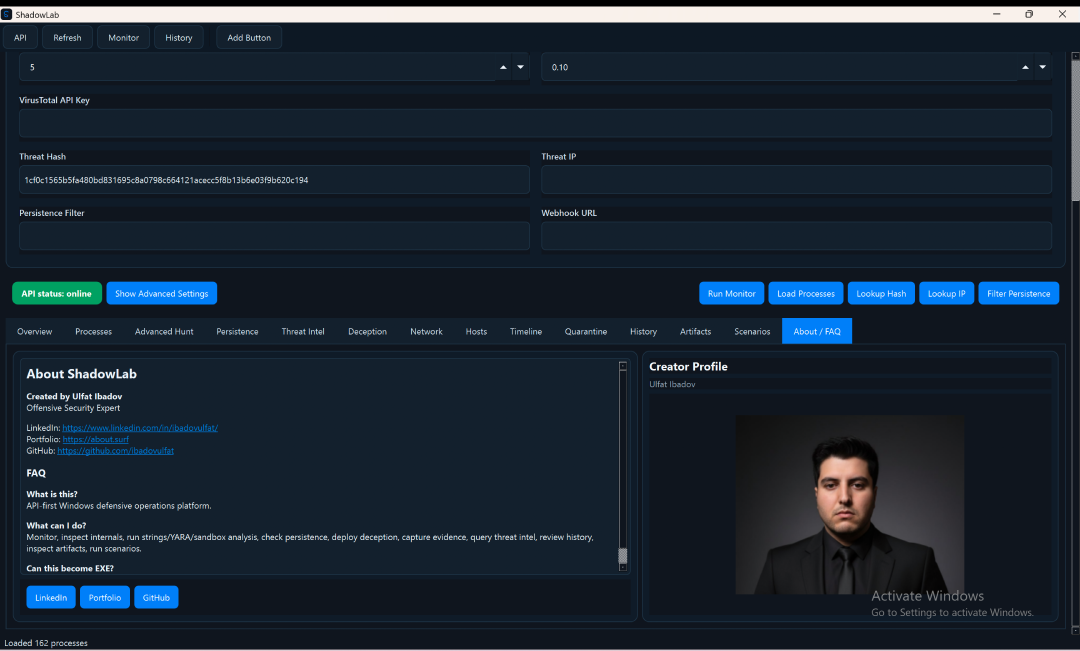
ShadowLab was rebuilt from a dashboard-centric prototype into an API-first security platform with a native operator experience.
The project now presents a more product-oriented architecture: FastAPI for orchestration and automation, PySide6 for the desktop surface, modular services for telemetry and response, and integrated workflows for incident review, quarantine, persistence, deception, and threat-intel enrichment.
Built by Ulfat Ibadov
Offensive Security Expert
ShadowLab is positioned as a Windows-focused defensive research platform for investigation, threat hunting, and response-oriented workflows. The goal is to present a serious security product direction rather than a simple dashboard demo.
